|
|
Content Assessment: Zero Trust Architecture Special Publication from NIST
Information - 95%
Insight - 95%
Relevance - 95%
Objectivity - 100%
Authority - 100%
97%
Excellent
A short percentage-based assessment of the qualitative benefit of the recent post sharing NIST's new special publication on Zero Trust Architecture.
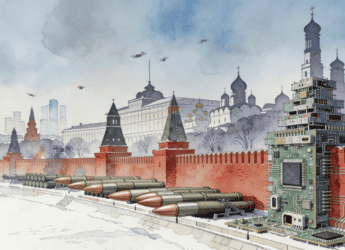
Editor’s Note: According to the recently published Zero Trust Architecture Special Publication from NIST, a typical enterprise’s infrastructure has grown increasingly complex and a single enterprise may operate several internal networks, remote offices with their own local infrastructure, remote and/or mobile individuals, and cloud services. The publication goes on to note that this complexity has outstripped legacy methods of perimeter-based network security as there is no single, easily identified perimeter for the enterprise. It is this complex enterprise that has led to the new model for cybersecurity, Zero Trust, which is described, defined, and discussed in this new NIST publication.
Zero Trust Architecture
Authored by Scott Rose, Oliver Borchert, Stu Mitchell, and Sean Connelly
Abstract
Zero trust (ZT) is the term for an evolving set of cybersecurity paradigms that move defenses from static, network-based perimeters to focus on users, assets, and resources. A zero trust architecture (ZTA) uses zero trust principles to plan industrial and enterprise infrastructure and workflows. Zero trust assumes there is no implicit trust granted to assets or user accounts based solely on their physical or network location (i.e., local area networks versus the internet) or based on asset ownership (enterprise or personally owned). Authentication and authorization (both subject and device) are discrete functions performed before a session to an enterprise resource is established. Zero trust is a response to enterprise network trends that include remote users, bring your own device (BYOD), and cloud-based assets that are not located within an enterprise- owned network boundary. Zero trust focuses on protecting resources (assets, services, workflows, network accounts, etc.), not network segments, as the network location is no longer seen as the prime component to the security posture of the resource. This document contains an abstract definition of zero trust architecture (ZTA) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture.
Operative Definitions
Zero trust (ZT) provides a collection of concepts and ideas designed to minimize uncertainty in enforcing accurate, least privilege per-request access decisions in information systems and services in the face of a network viewed as compromised.
Zero trust architecture (ZTA) is an enterprise’s cybersecurity plan that utilizes zero trust concepts and encompasses component relationships, workflow planning, and access policies. Therefore, a zero trust enterprise is the network infrastructure (physical and virtual) and operational policies that are in place for an enterprise as a product of a zero trust architecture plan.
Read the Complete Special Publication on Zero Trust Architecture (PDF)
NIST.SP.800-207-Zero-Trust-ArchitectureRead more on NIST Zero Trust Architecture
Additional Reading
- Challenged by Privacy? The NIST Privacy Framework
- New from NIST: Integrating Cybersecurity and Enterprise Risk Management (ERM)
Source: ComplexDiscovery