Editor’s Note: The recent unveiling of over 570 leaked documents from the Chinese security firm I-Soon provides an unprecedented glimpse into the intricate web of global cyber espionage activities purportedly linked to the Chinese government. This revelation highlights the sophisticated operations targeting a diverse array of entities, including foreign governments, NGOs, telecommunications firms, and minority groups. With insights into I-Soon’s extensive arsenal of cyber tools and the financial dealings behind its espionage contracts, this leak underscores the profound implications of state-sponsored hacking efforts on international security and the digital threat landscape. For professionals in cybersecurity, information governance, and eDiscovery, understanding the dynamics of such covert operations is crucial for devising effective defense strategies in an increasingly complex digital arena.
Content Assessment: Leaked Docs Unveil China's Pervasive Cyber Espionage: Insights into Hacker-For-Hire Firm I-Soon
Information - 92%
Insight - 91%
Relevance - 90%
Objectivity - 91%
Authority - 92%
91%
Excellent
A short percentage-based assessment of the qualitative benefit expressed as a percentage of positive reception of the recent article from ComplexDiscovery OÜ's cybersecurity beat titled, "Leaked Docs Unveil China's Pervasive Cyber Espionage: Insights into Hacker-For-Hire Firm I-Soon."
Industry News – Cybersecurity Beat
Leaked Docs Unveil China’s Pervasive Cyber Espionage: Insights into Hacker-For-Hire Firm I-Soon
ComplexDiscovery Staff
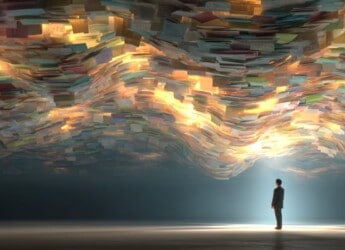
A compilation of leaked documents has shone a penetrating light on the activities of the Chinese security firm I-Soon, a private contractor entwined with the Chinese government’s extensive cyber espionage network. This leak, comprising over 570 documents and posted uniquely to the file-sharing platform GitHub, offers critical insights into the operations, targets, and tools of a company at the forefront of China’s global hacking campaigns.
In a detailed reveal, these leaked documents purport to show I-Soon’s involvement in sophisticated surveillance and hacking operations aimed at an array of targets: foreign governments, including Taiwan, India, South Korea, Malaysia, and Thailand; international NGOs such as Amnesty International and Chatham House; telecommunications firms; and minority groups like the Uyghur Muslims. Confirmations from independent cybersecurity experts, endorsements by significant cybersecurity firms such as SentinelLabs, and statements from internal sources lend credibility to the authenticity of these documents.
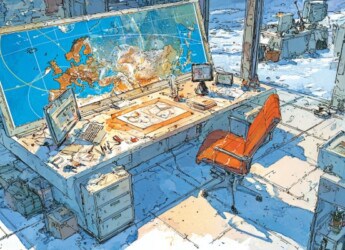
Central to the revelation is I-Soon’s purported arsenal of tools. The documents reveal technological enablers, offering remote control, data encryption, password cracking, two-factor authentication bypass, and precision tracking capabilities across the Apple, Android, Windows, and Linux platforms. This suite has, according to the leaks, been made available to various Chinese government bodies, including the Ministry of Public Security and the PLA. Notably, the financial records within these leaks show that espionage contracts have been lucrative, ranging from fees as modest as $15,000 for hacking Vietnamese police websites to up to $278,000 for monitoring dissidents’ social media.
The implications of these activities are profound. Revealing a network of hackers for hire, underpinning China’s state-sponsored hacking initiatives, the leaks underscore the asymmetric breadth of China’s cyber capabilities vis-a-vis its global counterparts. Analyst John Hultquist, chief analyst of Mandiant Intelligence, encapsulated the moment’s gravity, stating, “We rarely get such unfettered access to the inner workings of any intelligence operation. We have every reason to believe this is the authentic data of a contractor supporting global and domestic cyber espionage operations out of China.”
On the geopolitical spectrum, the hacking activities bear national security implications, with military strategists noting the potential utility of stolen information, such as Taiwan’s road maps and telecommunications data, in hypothetical Chinese military offensives. The intimate details of I-Soon’s alleged engagements suggest a hidden front in cyber warfare, one reflecting China’s digital advancement ambitions and, according to some officials, an enhanced threat landscape.
However, amidst these strategic maneuvers, internal tensions at I-Soon have been revealed. Conversations between executives and employees discuss financial difficulties, stagnating salaries, and a workforce eyeing exit doors, painting a less than idyllic picture of the cyber espionage sector.
In response to the unfolding events, Chinese authorities have initiated an investigative foray into the leaks, whereas I-Soon has retreated from the digital limelight, pulling its website offline. The broader intent and identity behind the leaks remain shrouded in mystery, as do the full extent and ramifications of I-Soon’s operations. Yet, what remains incontrovertible is the stark mirror these leaks hold up to the complexity and penetration of global cyber espionage.
This report unspools a narrative that goes beyond code and cyberattacks; it’s one where human ambition, geopolitical rivalry, and the omnipresence of digital threats converge, offering a cautionary tale to a world ever more embroiled in the virtual fray – and a precedent that tech and security audiences monitor with acute alertness.
News Sources
- Document leak exposes China’s reliance on offensive cyber firms
- Leaked Documents Shed New Light On China’s Sweeping Surveillance State
- Chinese Security Firm Document Dump Reveals Spying Methods
- Reported Leak of Chinese Hacking Files Supports US Warnings
Assisted by GAI and LLM Technologies
Additional Reading
- The Cyber Siege: China’s Expanding Digital Dominance and US Response
- EU Cybersecurity Investment Trends: Insights from the NIS Investments Report 2023
Source: ComplexDiscovery OÜ