|
|
Content Assessment: From Proactive Detection to Data Breach Reviews: Sensitive Data Discovery and Extraction with Ascema
Information - 90%
Insight - 90%
Relevance - 95%
Objectivity - 85%
Authority - 90%
90%
Excellent
A short percentage-based assessment of the qualitative benefit of the newly published service overview of Ascema Data Discovery and extraction.
Editor’s Note: From time to time ComplexDiscovery highlights publicly available service and product content from data discovery and legal discovery providers as an information service for the readers of its blog. While ComplexDiscovery highlights this content, it does not assume any responsibility for content assertions.
To submit recommendations for inclusion in ComplexDiscovery’s service and product content updates, contact us today.
Ascema Sensitive Data Discovery and Extraction
Provider: GeoLang (UK-based Cybersecurity Solution Provider)
Offering Information Shared with the Permission of GeoLang
Snapshot and Example Use Cases
The Ascema Sensitive Data Discovery platform accurately locates sensitive data and intellectual property across a multitude of data repositories such as endpoints, servers, external drives, USBs, Office 365, and cloud storage environments including IONOS, AWS, and Azure. This capability allows for a variety of use cases for legal, business, and information technology professionals in the eDiscovery ecosystem to include:
- Proactive location, analysis, review, notification, and extraction of sensitive and high-value data in real-time across live enterprise environments.
- Reactive data breach review (analysis, review, notification, and extraction) of compromised data for sensitive and high-value data.
Why Sensitive Data Discovery and Extraction?
Data protection tools can – and should – enhance a human-lead decision-making process. Current security solutions typically result in thousands of lines of reports that are then fed into Security Information and Event Management (SIEM) systems which, in turn, churn out yet more data.
Ascema Data Discovery and Extraction offers a powerful solution to what is becoming an increasingly prevalent problem. Instead of ever more lines of reports, sensitive data remediation is provided by end-users via elegant alerts and simple to use dashboard. Highly automated with dual reporting, security teams are now confident that sensitive data is being managed effectively by data owners themselves.
Data Discovery: The First Critical Step Before Data Extraction
Ascema identifies sensitive and regulated data both at rest and in transit. Automated and flexible search task options use a combination of pre-defined rules, bespoke regular expressions, and complex queries.
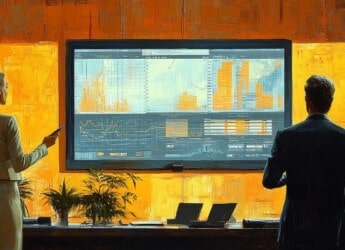
Data discovery and extraction has never been simpler. Once extracted the repository matches can be easily reviewed in context for further filtering. Sub-searches and compound queries are simple to perform with outputs either to targeted repositories, in the cloud or on-premise, as well as being downloadable or exported in a variety of formats. Enterprise reporting via user-friendly dashboards and the dynamically generated Data Discovery Executive Summary (HERO Report) provide additional data visibility to ascertain data threat patterns and user activity in real-time and offer flexible remediation options such as alert, quarantine or remove.
Key Features
- Simple and Elegant to Deploy and Use
- Highly Automated Remediation Capabilities
- Easy Data Discovery and Extraction
- Dynamically Generated Board Level Reporting
Key Benefits
- Gather Deep and Actionable Insight into Your Sensitive Data
- Complete Data Visibility Across Your Digital Estate
- Automatically Alert Users to Sensitive Data Stored Across the Enterprise and Apply Appropriate Remediation
- Support Regulatory Compliance and Standard Requisites through Automated Sensitive Data Discovery and Extraction
- Secure Data Through the Real-Time Application of Protective Controls Including Sync Folders and USBs
- Continuous and Comprehensive Data Monitoring
- Understand Your Organization’s Sensitive Data Risk Posture
- Supports Digital and Data Transformation Processes
Ascema Sensitive Data Discovery
- Pre-Configured and Customizable Search Patterns
- Compatibility with Windows, Linux, MacOS, and Cloud including AWS, Azure, Google, Office 365, Exchange, and SharePoint
- Comprehensive Data Monitoring both At-Rest and In-Motion
- Automated and Flexible End User or Administrator Remediation
- Active, Passive, Stealth, and Forensic Modes
Ascema Sensitive Data Extraction
- Search and Extract Unstructured Data
- Quickly Review Results in Context for Further Filtering
- Extract Individual Files with Sensitive Data from Container Files
- Filter Results and Create Further Repositories and Sub Repositories
- Target Repositories or Download in a Variety of Formats
- Unified Search and Reporting Interface for Endpoints, File Servers, Alfresco, and O365 Apps
- Export to SIEMS (e.g., Splunk)
- Easily Create New Tasks Based on Previous Tasks
- Pattern Specific Default Confidence Levels Lowers False Positives
Learn More About Ascema
- Request a Demonstration of Ascema Data Discovery: click here.
- Request a Free Trial of Ascema Data Discovery: click here.
- View a Sample of the Sensitive Data Discovery Executive Summary (HERO Report): click here.
About GeoLang
GeoLang, as part of the Shearwater Group plc, is a UK-based cybersecurity solution provider whose award-winning Ascema platform provides an easily deployed next-generation Sensitive Data Discovery, DLP, and Classification solution.
With the unique ability to protect, detect and remediate at a True Content level on-premise, across cloud-based services and beyond, organizations can now gain real value from open collaboration and information sharing without the fear of losing control of their high-value information.
- Website: GeoLang.com
- Email: Contact@GeoLang.com
- Phone: +44 (0) 2920 647012
- Corporate Headquarters: GeoLang Limited, Cardiff Business Technology Centre, Senghenydd Road, Cardiff. CF24 4AY
Additional Reading
- Data Lakes: An Important Technological Approach for Data and Legal Discovery
- Automating eDiscovery: A Strategic Framework
Source: ComplexDiscovery