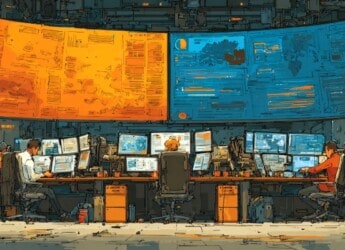
PowerSchool Data Breach Highlights Urgent Cybersecurity Needs in Education Sector
The PowerSchool data breach, affecting millions across the education sector, highlights the urgent need for enhanced cybersecurity measures. Discover how this incident unfolded, its implications, and lessons for protecting sensitive…