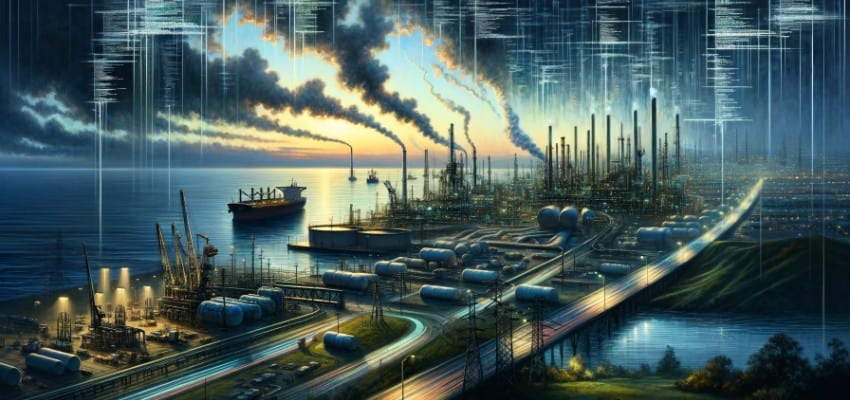
Editor’s Note: In May 2023, the cybersecurity community was alerted to a sophisticated cyber-espionage campaign, Volt Typhoon, targeting critical American infrastructure. Orchestrated by state-sponsored actors from China, this operation penetrated systems essential to the nation’s economic and security well-being, including West Coast ports, oil pipelines, and Texas’s power grid. The revelation, initially brought to light by Microsoft’s cybersecurity team and later corroborated by “Five Eyes” intelligence agencies, underscores a chilling reality: the digital battleground extends far beyond the confines of cyberspace, threatening the very fabric of societal function.
The Department of Justice (DOJ) and the Federal Bureau of Investigation (FBI)’s announcement last week of disrupting Volt Typhoon underscores the monumental efforts required to counteract such pervasive threats. This campaign, characterized by the technique of “living off the land,” reveals a strategic pre-positioning of cyber assets by adversaries to potentially cripple critical infrastructure in times of conflict. The implicated vulnerabilities in older network routers, primarily Cisco and Netgear, highlight a broader issue of cybersecurity in legacy systems, prompting a reevaluation of security practices and infrastructure resilience.
Content Assessment: FBI Unveils Disruption of Chinese Cyber Campaign Affecting U.S. Infrastructure
Information - 96%
Insight - 93%
Relevance - 91%
Objectivity - 90%
Authority - 92%
92%
Excellent
A short percentage-based assessment of the qualitative benefit expressed as a percentage of positive reception of the recent article from ComplexDiscovery OÜ titled, "FBI Unveils Disruption of Chinese Cyber Campaign Affecting U.S. Infrastructure."
Industry News – Cybersecurity Beat
FBI Unveils Disruption of Chinese Cyber Campaign Affecting U.S. Infrastructure
ComplexDiscovery Staff
In a landmark operation, the Department of Justice (DOJ) and the Federal Bureau of Investigation (FBI) announced Wednesday the disruption of a massive Chinese cyber-espionage campaign dubbed Volt Typhoon that penetrated critical American infrastructure systems.
Described by Microsoft’s cybersecurity team as being capable of disrupting critical communications infrastructure between the United States and the Asia region during future crises, Volt Typhoon was made public in May 2023 after being detected by the tech giant’s cybersecurity team. Additionally backed by “Five Eyes” intelligence agencies’ conclusions, the state-sponsored hackers from China were accused of developing capabilities to target West Coast ports, oil pipelines, and Texas’s power grid, among other critical infrastructures.
“Pre-positioning” cyber warfare assets to “disrupt or destroy that critical infrastructure in the event of a conflict” was made evident by the Cybersecurity and Infrastructure Security Agency (CISA) in December, according to their statement. Experts have cited Volt Typhoon as one of the top instances of “living off the land” – a technique where hackers infiltrate systems without causing damage or revealing their presence, and in this case, establishing a foothold for potential destructive attacks.
“They’re actively attacking our economic security, engaging in wholesale theft of our innovation and our personal and corporate data,” FBI Director Christopher Wray conveyed in a warning about the risk China’s activities pose to national security. Deputy Chief of the DOJ’s National Security Division, Sean Newell, explained that the hackers had created a network of compromised routers that enabled them to work in secrecy.
The FBI has determined these older Cisco and Netgear routers were “easy targets,” primarily because their security support had reached its end, making them particularly susceptible to exploitation. Wray also expressed concerns about China attempting to meddle in the upcoming 2024 elections, leveraging user data collected by Chinese applications to potentially facilitate espionage efforts.
Despite the successful disruption of Volt Typhoon, the vast scale of operations cast doubts within the cybersecurity community on the completeness of the disruption. The FBI’s efforts to remove the malicious software have left some experts advocating for complete router replacement as a more secure route.
Addressing manufacturing vulnerabilities, CISA and the FBI called on router producers to integrate security measures into the design and maintenance of their products. This includes adopting software updates automatically and minimizing the possibility of remotely disabling network security.
Pushing the boundaries of preventive cyber defense, United States officials dismantled another hacking operation with alleged links to China. They also spoke candidly about the future threats this kind of cyber warfare presents to civilian infrastructure. Wray’s testimony before the House Select Committee on the Chinese Communist Party revealed that while the focus remained on the broader strategic concerns, there was an urgent need to concentrate on actual cyber threats that could disrupt everyday American lives.
Given China’s adeptness at remaining undetected within computer systems, Easterly, the director of CISA, highlighted the immediate need for attention to these threats, which could induce societal panic and complicate effective crisis responses.
Amid these revelations, lawmakers are looking to bolster cybersecurity measures within the defense industrial base. With the Ivanti VPN product vulnerabilities coming to light and eliciting responses from various defense contractors, the National Security Agency acknowledged investigations into potential intrusions. Even as the Defense Department amps up requirements for cybersecurity in contracts, there is a growing call within Congress for increased investment in the FBI’s cyber capacities.
After warnings by intelligence chiefs from the Five Eyes alliance regarding China’s technological advances in hacking and intellectual property theft, the risk landscape for U.S. critical infrastructure remains in flux. U.S. Attorney General Merrick Garland emphasized the importance of disassembling malicious operations that threaten American security.
As we edge closer to the 2024 presidential election, tensions intensify not only in the geopolitical arena but also within the realm of cyber warfare. With China’s consistent efforts to gain a cyber advantage and the U.S. striving to improve its defensive capabilities, the cyber threat landscape is set to remain a significant factor in the proceeding years of strategic competition.
News Sources
- FBI Finds Chinese State Hacker Malware on Hundreds of U.S. Infrastructure-Related Routers
- US says it blocked China cyber-threat but warns hackers can ‘wreak havoc’
- Major US Counter-Hack Disables China Botnet in Critical Infrastructure
- Defense contractors investigating potential Ivanti zero-day hacks
- Critical infrastructure is underprepared to face China’s hacking powers
Assisted by GAI and LLM Technologies
Additional Reading
- The Cyber Siege: China’s Expanding Digital Dominance and US Response
- Cultivating ‘Guarded’ Digital Personas: Why Cyber Vigilance Matters More Than Ever
Source: ComplexDiscovery