Weaponizing Security? The Emerging Role of the CISO in eDiscovery
The role of the Chief Information Security Officer (CISO) is becoming the norm in eDiscovery companies as these companies grow their client base and venture into compliance and data breach…
Pivotal Acquisition Corp. to Merge with KLDiscovery
Pivotal Acquisition Corp., a public investment vehicle, and KLDiscovery, a global provider of electronic discovery and information governance services to Fortune 500 companies and top law firms, announced on May…
Time For Outsourcing? A Look At BPO That Might Inform LPO
The main opportunity to push for greater innovation and to draw on specialist capabilities obviously comes at contract time, and there is good news here. To keep up with rapidly…
A Security Cause to Pause: The Microarchitectural Data Sampling (MDS) Vulnerability
A new group of Intel vulnerabilities, collectively called Microarchitecture Data Sampling (MDS), were disclosed last week. The vulnerabilities allow attackers to steal data as processes run on most machines using…
Five Great Reads on Data Discovery and Legal Discovery for May 2019
A selection of five articles shared regularly to inform and update legal and information technology professionals on the art and science of data discovery and legal discovery.
NPS: You May Want to Know More About This Important Number
A Net Promoter Score®, commonly referred to as NPS®, is a straightforward metric that measures customer experience and appears to be a predictor of company growth. Based on the importance of…
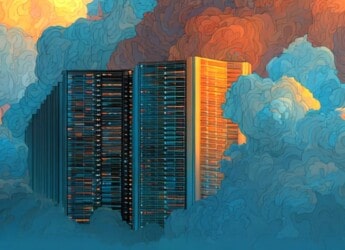
Federal IT Investments and the Cloud in FY 2020
According to the IT Dashboard, federal agencies expect to invest a combined $1.6 billion in cloud infrastructure as a service (IaaS) and platform as a service (PaaS), $924 million in…
BSA Releases Framework for Secure Software
The BSA Framework for Secure Software tackles complex security challenges through an adaptable and outcome-focused approach that is risk-based, cost-effective, and repeatable. The Framework describes baseline security outcomes across the…
A Practical and Looming Danger? SHA-1 Collision Attacks
The work that Thomas Peyrin and his colleague, Gaetan Leurent, have done goes far beyond just proving SHA-1 chosen-prefix collision attacks are theoretically possible. They show that such attacks are…
A 2019 Legal Technology Salary Mashup
The 2019 Legal Technology Salary Mashup shares an aggregation of general salary data points from publicly available research, reports, and industry observations that may be beneficial for use by legal…