Editor’s Note: Critical infrastructure defenders across Europe are facing a more urgent reality: cyberattacks do not need to trigger physical destruction to achieve strategic impact. The attempted intrusion at Poland’s National Centre for Nuclear Research underscores how nation-state cyber activity is increasingly focused on institutions where operational resilience, sensitive data, and public trust converge. For cybersecurity, data privacy, regulatory compliance, and eDiscovery professionals, the incident serves as a timely reminder that effective defense depends on more than perimeter security alone. IT/OT segmentation, incident response readiness, cross-agency coordination, and disciplined information governance all play a central role in limiting risk and preserving resilience when high-consequence institutions become targets.
Content Assessment: When the Atom Becomes the Target: Poland's Nuclear Research Centre Repels a Cyberattack
Information - 93%
Insight - 92%
Relevance - 90%
Objectivity - 92%
Authority - 90%
91%
Excellent
A short percentage-based assessment of the qualitative benefit expressed as a percentage of positive reception of the recent article from ComplexDiscovery OÜ titled, "When the Atom Becomes the Target: Poland's Nuclear Research Centre Repels a Cyberattack."
Industry News – Cybersecurity Beat
When the Atom Becomes the Target: Poland’s Nuclear Research Centre Repels a Cyberattack
ComplexDiscovery Staff
Hackers don’t need to split the atom to cause a meltdown — they just need to breach the network that controls it.
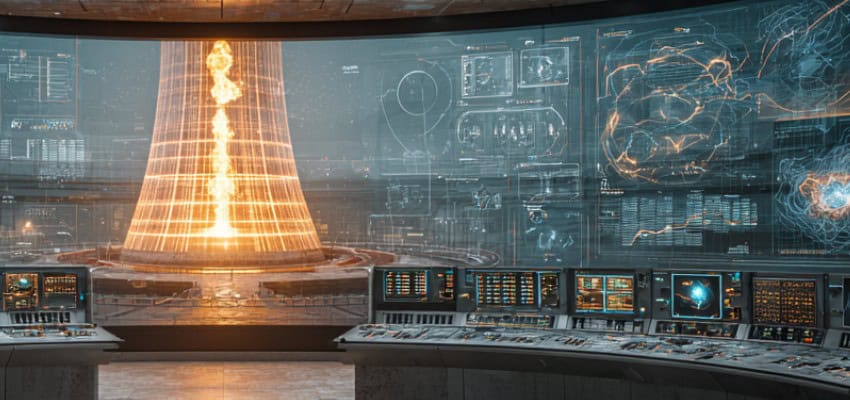
That unsettling reality came into sharp focus on March 12, 2026, when Poland’s National Centre for Nuclear Research (NCBJ) confirmed it had repelled an attempted intrusion into its IT infrastructure, a cyber incident that drew immediate attention from government ministries, national intelligence services, and security professionals across Europe. The attack was detected and blocked before causing any impact, with NCBJ’s security systems and internal procedures preventing the compromise and allowing its IT staff to quickly secure targeted systems. The outcome was reassuring. The context surrounding it was not.
The NCBJ, located in Otwock-Świerk approximately 25 kilometers southeast of Warsaw, is Poland’s preeminent government nuclear science institution and one of the largest scientific institutes in Central Europe. It operates the country’s only nuclear research reactor, MARIA, and conducts research in nuclear and particle physics, reactor technology, radiopharmaceuticals for medical applications, and industrial and environmental applications. The facility does not engage in military-related activities, and Poland maintains no nuclear weapons program. That makes the targeting of the NCBJ less about weapons and more about something equally consequential in the modern threat landscape: data, disruption, and the pressure that comes from demonstrating a state’s most sensitive institutions are reachable.
Following the detection of the attack, the research centre began working closely with national cybersecurity authorities and other relevant services to analyse the event and strengthen protections. Professor Jakub Kupecki, Director of the NCBJ, moved quickly to reassure a nervous public. “No production, operational or research processes were disrupted, and the MARIA reactor operates safely and without disruptions, at full power,” Kupecki stated.
A Multi-Front Digital War Over Polish Infrastructure
To understand this attack in isolation is to misread it entirely. The assault on Poland’s nuclear research centre did not materialize from a vacuum. It arrived as part of a sustained campaign against Polish national infrastructure that has accelerated over the past year with alarming velocity.
A cyberattack targeting Poland’s power grid in late December 2025 has been linked to the Russian state-sponsored hacking group Sandworm, which deployed a new destructive data-wiping malware during the attack. According to ESET, which analyzed the malware and named it DynoWiper, the attack is attributed to the Russia-aligned Sandworm APT with medium confidence, based on a strong overlap with previous Sandworm wiper activity — though researchers noted they were not aware of any successful disruption occurring as a result. Dragos separately noted that the disabling of certain OT or industrial control system equipment beyond repair moved what could have been seen as a pre-positioning attempt into an attack with lasting physical consequences. That distinction matters: ICS equipment rendered permanently inoperable without a visible blackout is precisely the kind of quiet, durable sabotage designed to complicate long-term operational resilience while evading immediate public scrutiny.
According to an ICCT report cited by BleepingComputer, Poland ranked high on the target list of Russian cyber-actors, with 31 confirmed hybrid warfare incidents attributed to them between mid-2025 and early 2026. Against this backdrop, the attempted intrusion at Poland’s National Centre for Nuclear Research (NCBJ) marks a concerning evolution: while attribution remains under investigation, early reporting suggests indicators pointing to Iran or possible false‑flag activity, highlighting that Poland’s threat landscape may now involve additional potential nation‑state adversaries beyond Russia.
Reporting by Reuters, published March 12, 2026, revealed that Polish authorities are examining indicators pointing toward Iranian involvement. Minister for Digital Affairs Krzysztof Gawkowski told private broadcaster TVN24+ that the attack had taken place “in the past few days,” adding: “The attack may not have been on a huge scale, but there was an attempt to break through the security that was stopped. Appropriate services are already working.” On the question of origin, Gawkowski stated that “the first identifications of the entry vectors, i.e., those places from which the centre was attacked, are related to Iran,” while cautioning that those indicators could represent a false flag deliberately planted to conceal the attackers’ true location.
One detail sharpens the complexity of that attribution question. Poland’s Deputy Prime Minister and Minister of National Defence, Wladyslaw Kosiniak-Kamysz, had earlier made Poland’s position on the Iran-U.S.-Israel conflict unambiguous. “No such request has been made. Poland is not participating in this operation,” Kosiniak-Kamysz stated, addressing questions about whether NATO members could be drawn into the widening Middle East conflict. If Poland maintains no formal role in that conflict, the question of why Iranian actors would direct resources toward Polish nuclear infrastructure is not self-answering. Analysts broadly assess that Iranian target selection often reflects geopolitical signaling — the choice of a NATO-member nuclear institution carrying symbolic weight that extends beyond any specific operational objective — though definitive attribution in this case remains open.
Iran’s Expanding Cyber Footprint in Europe
The geopolitical backdrop surrounding a potential Iranian connection to the NCBJ attack demands context rather than assumption. On February 28, 2026, tensions that had been simmering for years erupted into a full-blown conflict involving the Islamic Republic of Iran, the United States, and Israel. In the weeks that followed, Iranian-aligned cyber actors dramatically expanded the geographic scope of their operations.
Iranian state actors, proxies, and hacktivists ideologically aligned with Iran orchestrated cyberattacks against perceived adversaries during the 12-day war in 2025, complete with reconnaissance, recruitment, defacement, data theft, data dumps, phishing, and malware delivery. That campaign has broadened substantially since the February 2026 escalation. According to analysis published by legal and risk consultancy Kennedys Law, as of early March 2026, security researchers tracked over 60 active threat groups aligned with the conflict — 53 of them operating on the pro-Iranian side — and activity has accelerated sharply, with adversary operations intensifying rather than diminishing contrary to some initial assessments that Iranian cyber capabilities had been degraded by kinetic strikes.
What makes Iran a formidable cyber adversary is its unpredictability paired with the scope of its digital resources and preparation. Iranian cyber actors are known for laying the groundwork for cyberattacks and influence operations months or even years before geopolitical tensions escalate. This long-horizon preparation is a documented pattern across multiple Iranian APT groups — not a claim specific to the NCBJ incident, for which no pre-positioned infrastructure has been publicly confirmed — but it is precisely what makes attribution so difficult and incident response so demanding when an attack does execute.
For cybersecurity professionals tracking the NCBJ incident, a specific behavioral pattern in Iranian state tradecraft warrants close attention, even as the precise responsible actor in this case remains unidentified. No group has claimed responsibility for the NCBJ intrusion, and investigators have not publicly confirmed which threat actor was involved. What is documented, however, is the broader Iranian APT playbook that defenders at research institutions and critical infrastructure organizations should be planning against. According to threat intelligence firm Trellix, APT42, an Iranian state-sponsored threat actor operating on behalf of the IRGC and active since at least 2015, has long pursued a tradecraft centered on social engineering and credential harvesting rather than heavy reliance on disk-based malware. The group’s hallmark approach involves cultivating trust with high-value targets through sustained personal engagement before attempting to compromise their accounts or devices. This profile is corroborated independently by Mandiant, which documented APT42 posing as journalists and event organizers to build trust with victims through ongoing correspondence, using these social engineering schemes to harvest credentials and gain initial access to cloud environments. Security teams should be actively reviewing their identity governance posture — not just perimeter defenses — and ensuring privileged access management controls are current and regularly audited. The attack surface that matters most against this class of adversary is often not a firewall gap but a set of over-privileged credentials belonging to a trusted collaborator.
The IT/OT Divide: A Security Architecture That Held
Perhaps the most instructive dimension of the NCBJ incident is what did not happen. Despite a successful intrusion attempt against IT systems, the MARIA reactor’s operational technology (OT) environment remained completely isolated and unaffected. This outcome reflects a deliberate architectural decision that every critical infrastructure operator should examine closely.
Nuclear research institutions present adversaries with a dual prize: access to sensitive scientific data and the reputational weight of being publicly associated with a breach. Even an intrusion that never reaches operational systems can serve an adversary’s goals, because the public record of the attempt itself communicates vulnerability to audiences far beyond the target organization. For state-level actors pursuing geopolitical pressure rather than immediate operational disruption, generating a credible headline may be sufficient return on the investment.
The separation of IT and OT environments — network segmentation — is not new doctrine, but it remains inconsistently applied across industries. Organizations that manage sensitive research, operate physical machinery, or store regulated data should treat IT/OT segregation as a foundational requirement, not an advanced capability. Cybersecurity professionals advising clients in energy, healthcare, utilities, or defense contracting should be having this conversation at the executive and board level now, not following an incident. Building the argument for segmentation after a breach is a significantly harder conversation.
The speed of detection at NCBJ was equally instructive. The monitoring and response procedures in place caught the intrusion and contained it before it could propagate through the network — a result that reflects disciplined investment in detection architecture and rehearsed response procedures rather than fortunate timing. Organizations that rely on signature-based detection alone, without behavioral analytics configured to flag anomalies against a known baseline of normal network activity, are operating with a meaningful blind spot against the kind of credential-based, low-noise intrusion techniques prevalent across Iranian APT operations. Security practitioners broadly recognize that investing in detection capability before an incident occurs is substantially less costly — operationally, legally, and reputationally — than responding to a breach that succeeded.
Government Coordination as a Security Multiplier
The NCBJ’s response demonstrated something that is frequently undervalued in post-incident analysis: the operational value of pre-established government coordination frameworks. The institute coordinated its response with several government bodies, including NASK-PIB, the Ministry of Digital Affairs, Deputy Prime Minister Krzysztof Gawkowski, and the Ministry of Energy to ensure the highest level of protection for critical infrastructure.
This is not bureaucratic procedure for its own sake. In a hybrid warfare environment where threat actors move quickly and formal attribution takes time, pre-negotiated channels between research institutions, national cybersecurity agencies, and energy ministries compress the response timeline from days to hours. Organizations in both the public and private sector should invest in building those relationships before incidents occur. Knowing precisely who to contact and through which channel when a network is under active attack is a security asset as concrete as any technical control.
From an information governance perspective, the NCBJ incident surfaces important questions about data stewardship in research environments. Institutions conducting nuclear physics research, isotope production, or classified-adjacent scientific work hold data that, in the wrong hands, carries consequences extending well beyond the institution itself. Ensuring sensitive research data is subject to classification policies, access controls with least-privilege enforcement, and documented retention schedules is not merely sound administrative practice — it is part of the institution’s active defensive posture. In a threat environment where state-level actors are specifically targeting intellectual property at scientific facilities, information governance and cybersecurity are not parallel disciplines. They are the same discipline viewed from different angles.
Implications for eDiscovery and Information Governance Professionals
The intersection of this incident with eDiscovery and information governance is direct and immediate. When a cyberattack targets a critical infrastructure operator or government-affiliated research institution, post-incident regulatory and legal exposure can be substantial. The European Union’s NIS2 Directive activates a strict three-stage reporting clock: an early warning to the relevant national authority or CSIRT within 24 hours of becoming aware of a significant incident, a full incident notification within 72 hours, and a comprehensive final report within one month. Organizations that have not pre-mapped their data environments — knowing exactly what data exists, where it resides, who has access, and how it is classified — will be constructing that documentation under legal deadline pressure while simultaneously managing an active security response.
Litigation holds, forensic preservation, and chain-of-custody protocols become immediately relevant the moment an organization has reasonable grounds to believe a breach may have occurred. Information governance professionals who have built those workflows and stress-tested them against realistic incident scenarios will be positioned to support legal and compliance teams without compounding an already complex situation. Those who have not will find themselves building the framework from scratch under the worst possible conditions.
Maintaining comprehensive, audit-ready logs is another foundational requirement the NCBJ incident reinforces. Effective forensic investigation depends entirely on log integrity and availability. Organizations should verify now that logging is enabled across all critical systems, that log data is protected from tampering or deletion, and that retention periods align with both regulatory requirements and the realistic timelines of litigation and regulatory proceedings. Log gaps are not a minor technical oversight — they are a legal liability and an investigation failure waiting to happen.
A Threat Landscape That Does Not Stand Still
The NCBJ incident is a snapshot of a threat environment in rapid evolution. Poland finds itself simultaneously in the crosshairs of two sustained nation-state cyber campaigns targeting European infrastructure — Russian hybrid warfare operations against energy and defense systems, and Iranian-aligned cyber operations expanding across NATO-adjacent nations in the wake of the February 2026 escalation. According to threat intelligence firm Palo Alto Networks’ Unit 42, state-sponsored campaigns might target their victims’ supply chains, critical infrastructure, vendors, or providers, and a multi-layered defense is the most effective posture, as no single tool can provide complete protection.
Cyber operations in 2026 have become the connective tissue between geopolitical confrontation and civic daily life, translating state-level competition into disruptions felt directly across power grids, research institutions, healthcare networks, and the financial systems that citizens and organizations depend on to function. That framing should inform how every organization — not only nuclear research centres — approaches security investment, governance posture, and incident readiness planning.
The NCBJ held the line. The reactor kept running. The data remained protected. But the adversaries behind this attack are already evaluating what they learned from one unsuccessful intrusion — and they are not deterred by a failure when that failure still teaches them something about how quickly the defender responds, which alarms fire, and where the boundaries of the segmented network actually lie.
If your most capable adversary attempted to breach your systems tomorrow, would your detection find it before your data did?
News Sources
- Poland says ‘many indications’ foiled cyberattack on nuclear center originated in Iran (The Times of Israel)
- Poland’s Nuclear Research Centre Targeted by Cyberattack (BleepingComputer)
- Hacking Attempt Reported at Poland’s Nuclear Research Center (SecurityWeek)
- Wiper Attack on Polish Power Grid Linked to Russia’s Sandworm (Infosecurity Magazine)
- Poland Power Grid Attack: ELECTRUM Targets Distributed Energy (Dragos)
- Hackers Tried to Breach Poland’s Nuclear Research Centre (Help Net Security)
- Iran and the Expanding Cyber Front: What Government Leaders Need to Know (SC Media)
- First Cyberattacks of War Hint at Iran’s Playbook Against U.S. (Axios)
- Uncharmed: Untangling Iran’s APT42 Operations (Mandiant / Google Cloud)
- The Iranian Cyber Capability 2026 (Trellix)
Assisted by GAI and LLM Technologies
Additional Reading
- Cybersecurity Implications of the 2026 Middle East Escalation: When Cloud Infrastructure Becomes a Target
- The Gatekeeper’s Key: How the Conformity Assessment Unlocks the EU AI Market
- EDPB and EDPS Weigh In on the Digital Omnibus: Personal Data, Breach Reporting, and AI Governance
- 2026 AI Safety Report Flags Escalating Threats for Cyber, IG, and eDiscovery Professionals
- The Algorithmic Guardrail: National Defense in the Age of Autonomous Risk
- EU’s Preliminary DSA Findings Put TikTok’s Engagement Design in the Regulatory Crosshairs
- Market Reaction or Overreaction? Anthropic’s Legal Plugin and the Facts So Far
- Moltbook and the Rise of AI-Agent Networks: An Enterprise Governance Wake-Up Call
- From One-Eyed Kings to Collective Sight in Enterprise AI
Source: ComplexDiscovery OÜ
ComplexDiscovery’s mission is to enable clarity for complex decisions by providing independent, data‑driven reporting, research, and commentary that make digital risk, legal technology, and regulatory change more legible for practitioners, policymakers, and business leaders.